Practical Malware Prevention Strategies for Businesses
May 9, 2024 - Lou Farrell
Revolutionized is reader-supported. When you buy through links on our site, we may earn an affiliate commission. Learn more here.
Malware is becoming an increasingly severe problem that can disrupt business operations, result in data loss, cause customers to lose confidence and more. Although it’s a prominent cybersecurity threat, business leaders can use malware prevention strategies to reduce the chances of major issues.
Invest in Malware Prevention Training
A good starting point is for company decision-makers to teach employees how to participate in malware prevention every day. Many people are so accustomed to using the internet daily and having trouble-free experiences that they minimize the threats single malware attacks could cause in their organizations.
For example, some malware attacks start when someone merely clicks on a malicious link. One 2023 study found that almost 1 in 3 people would likely click those links or comply with fraud-driven requests.
Another valuable finding from the study is that the subject lines of malware-containing emails often feature subject lines related to human-resources topics, such as vacation time updates or dress code changes. That strategy makes sense from a cybercriminal’s point of view because they want to make the content seemingly relevant to as many people as possible.
Employees don’t want to risk getting managerial reprimands or being out of luck the next time they ask for time off while planning an upcoming vacation. Additionally, if the emails come from human resources or another department people will trust them without thinking. Then, hackers have the chance of broader reaches with every attack attempt.
Consider Realistic Simulations
Some malware prevention training programs try to catch participants by simulating common scam tactics. Then, a company’s IT department or other security team members can look for trends among response rates and reasons.
It’s also important that malware education reflects hackers’ updated and evolving methods. For example, Singaporean bank workers watched deepfake videos, including one made with artificial intelligence tools.
That exercise was a highly applicable way to learn how realistic attempts to spread malware can seem. If a person sees a video or hears an audio clip of their boss instructing them to do something, most would follow the order without question. The only problem is that a scammer may have been the one asking.
Aim to make the content as relevant as possible to different roles, file types, requests and more. The more readily employees can apply what they’ve learned to their real-life work environment, the more useful they should find the training.
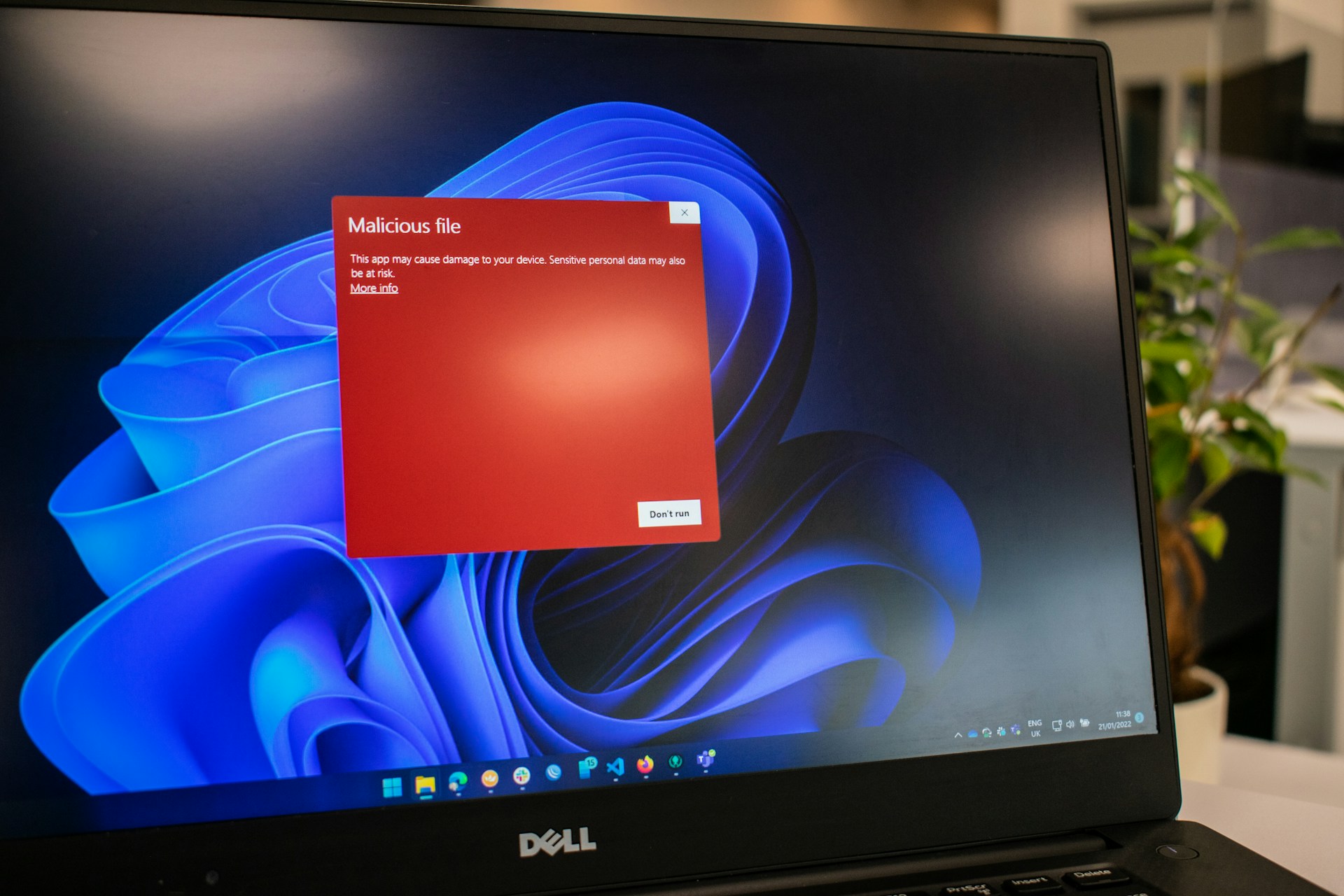
Ask People to Think Before Downloading Files
Another simple but effective malware prevention strategy is encouraging people to think critically before downloading files. What seems like a harmless work-related file could be malware in disguise.
People should ask things such as:
- Do I know the sender?
- Was I expecting this file attachment?
- Is the file in a recognizable format?
- Have I received similar attachments before?
Going through a brief but applicable checklist like that is a great way to break people’s habit of mindlessly clicking on attachments to download them. An unusual attachment is not a guaranteed sign of malware.
The sender might have accidentally attached the file, especially if they were working too quickly. However, unintentionally sending files to someone could create privacy issues depending on the content. That’s another reason it’s always best for people to stop and think about the validity of the file attachment before downloading it.
IT department members should also caution employees that malicious files do not always have strange extensions. One 2023 study identified a 53% increase in malware attacks involving common file types, such as Microsoft Word documents and PDFs. Researchers detected an average of 411,000 malicious files per day. That massive number emphasizes the need for people at businesses of all types and sizes to remain vigilant in their malware detection efforts.
Emphasize the Need to Verify Legitimacy
Phishing attacks have become incredibly diverse over the years. Whereas some involve compromising third-party sites, others use text messages. However, urgency is a common thread in these attacks.
Many phishing victims reveal they received messages that demanded they act immediately to avoid dire consequences. The content often centers on topics such as tax returns, paychecks, overdue bills or potential jail time. This tactic is an example of how cybercriminals may plant malware through phishing messages that get people to act without considering the consequences.
However, verifying a message’s authenticity can happen quicker than people may realize. That’s because many authoritative organizations have content that sets the record straight about potential phishing attacks.
For example, the Internal Revenue Service has website content clarifying it will never engage with taxpayers through email. So, if someone gets something in their inbox supposedly from the IRS, they can immediately realize it’s a scam and disregard it or report the content through the proper channels.
When checking a message’s authenticity, workers should never reply directly to emails received. That approach would mean they only engage with scammers who would likely concoct even more elaborate circumstances to trick unsuspecting individuals. Instead, the best approach is to find a genuine contact through other means.
If a suspicious email supposedly comes from Amazon, go directly to Amazon’s website by typing the URL into a browser and finding contact details there. Then, tell the customer service team about the message received and get their answer about whether it’s real.
Keep Operating Systems Updated
Many businesses have kept computers running on outdated operating systems for far too long. IT team leaders often justify that decision by determining that updating all operating systems at once will take a long time and be quite costly. That line of thinking is especially common in larger organizations or those with limited resources.
Running out-of-date operating systems is a risky choice from a malware prevention point of view. Developers release patches once they discover vulnerabilities hackers could exploit. However, some operating systems are so old that the companies behind them no longer provide those security patches or other updates. It then becomes especially difficult for IT teams to keep them well-protected as part of an overall cybersecurity plan.
Leaders can consider taking a staged approach if a company’s budget cannot accommodate purchasing operating system upgrades for all computers at once. One possibility is to address the most critical computers or those most vulnerable to hacking first.
Another option is to create a temporary policy that allows people to bring laptops from home. However, if decision-makers do that, they should have each computer screened by the IT team for security risks first.
Implement Malware Prevention Strategies Now
These tips show that people have various ways to reduce the chances of malware affecting their businesses. Moving forward with some of these suggestions is an excellent way to be proactive and emphasize that each employee plays a role in keeping the company safe from attacks.
Revolutionized is reader-supported. When you buy through links on our site, we may earn an affiliate commission. Learn more here.
Author
Lou Farrell
Lou Farrell, Senior Editor, is a science and technology writer at Revolutionized, specializing in technological advancements and the impacts on the environment from new developments in the industry. He loves almost nothing more than writing, and enthusiastically tackles each new challenge in this ever-changing world. If not writing, he enjoys unwinding with some casual gaming, or a good sci-fi or fantasy novel.







